Insights Poll: When It Comes To Content Security, How Sure Is Sure?
Can confidence breed complacency?
The recent news about the “Panama Papers” fiasco has many of us who work in legal concerned—again—with issues of content security. This most recent scenario, in which 11.5 million documents and 2.6 terabytes of data related to the super-secretive world of offshore banking found their way from a Panamanian law firm and into the public eye, only serves to highlight the sensitive nature of legal work – and the constant vigilance required to protect legal work product.
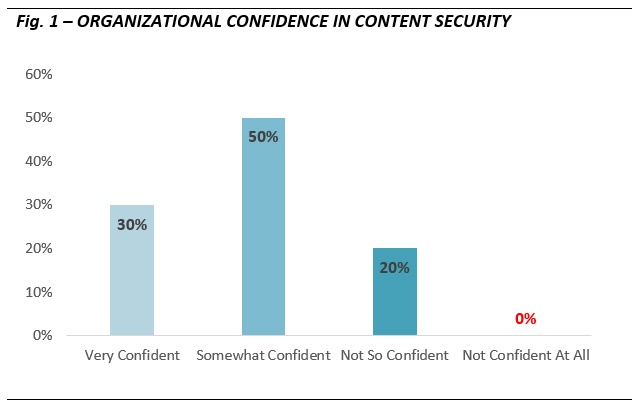
Last week, we asked our Hyperion Research community to weigh in on that vigilance, with a flash poll that asked, ”How confident are you that your systems and technologies keep your work product secure?”
The results (Fig. 1) produced a surprising finding. A full 80 percent of respondents expressed they were either somewhat or very confident that their content is secure. Even more surprising for a famously skeptical profession, not a single respondent felt unconfident in their content security – a remarkable demonstration of self-assurance. No one told us they have zero confidence in their security.
This expression of confidence correlates strongly, it seems, to our perplexing finding last year of the low priorities placed in Security as part of our Enterprise Content Management research. Despite all the hype and soundbites, could it be that, collectively, we’re much more confident about the safety of our confidential content than we should be, and so likewise far too complacent about the need for vigilance and security? Though in our ECM research last year we opined that users often confused network security with content security – the risk prevention tools and tactics to prevent hacks and unauthorized access versus the tools to secure and encrypt content at rest – we may very well have overlooked a very simple and very human phenomenon: that we tend to be confident about situations in which we do not perceive a problem.
The combination of lagging urgency and consequent overconfidence is a red flag for us all. The plight of Mossack Fonseca and the “Panama Papers” exposure of terabytes of confidential and privileged communications, work product, trade secrets and personally identifiable information – far more data pilfered than the Sony and Snowden breaches combined! — should give the legal industry serious pause. If the “super-secretive” guardians of offshore banking could fall victim to a simple attack, how can the rest of us sleep soundly at night?
We strongly suggest that now is an opportune time for legal organizations to revisit their current security protocols and tools. Content security is complex – never simple – and the methods of exposure are as varied as the types and locations of the content we have such strict duties to protect. We recommend multi-pronged strategies that incorporate readily available technologies, including encryption both at rest and in transit, two-factor authentication and integrations with Single Sign-On. Ensure that you are using the most up-to-date versions of your content, application, operating system and Web-based technologies. Mossack Fonseca, according to reports, used an outdated version of the Drupal open source Web content management system.
Remember, also, that many breaches occur not because of nefarious conduct, but because of well-meaning though uninformed insiders who expose data or access unwittingly. Clear, comprehensive information governance policies – and the tools to ensure and audit compliance – are just as important as firewalls and encryption.